Kalita Partners asked Chris Gould, Senior Cyber Adviser, and Alex Pisemskiy, Forensic Technology Leader, what the end lockdown means for Cyber Security and business.
Kalita Partners:
We’ve all heard about the increase of cyber-fraud during COVID-19. What is happening now when people are returning to work?
Chris Gould:
The way to answer this question is by asking “Who is coming back? What does that actually mean?”. While we see some people coming back to the office, we’re not seeing a massive shift back to normal office working. For a lot of people, work from home will still be the norm for a long period of time. Some of the challenges companies had to deal with in terms of opening up their core systems to remote access and providing access to their employees to work from home are still going to be with us for some time.
The fact that we start seeing people coming back to the office is not going to change the overall risk we’ve had to address with people being forced to work in a remote fashion.
Kalita Partners:
What new cyberthreats have risen during the pandemic?
Chris Gould:
The increase in cyber threats comes from a number of different areas. Opportunists are always out there looking to take advantage of anything when people are overwhelmed with fear and uncertainty. The massive prevalence of online phishing attacks using information about COVID-19 as an attraction to get people to click on links has risen.
It is interesting to look at this attraction phenomenon together with two elements. First, organisations have had to rapidly digitise their workforce and get their employees to work from home in ways they have not been used to doing before. Second, organisations have had to open up their core systems. This provides a greater risk and where there is risk, there is opportunity. Every measure taken by businesses to enable staff to work remotely has enhanced this risk because it has been done quickly and control systems were circumvented to enable remote working.
Alexander Pisemskiy:
When the COVID-19 pandemic arose, many companies were not ready to enable most workers to work from home. Their security perimeter blew up. Business continuity was considered a priority rather than the security of information and processes. Most people worked from their personal devices, which were untrusted, or brought home their corporate devices to their untrusted home networks, which got more interesting for different kinds of attackers.
When people will start to come back to the office, the question will be “How will the CISO (Chief Information Security Officer) handle the fact that most end-user devices have gone into untrusted mode? How will they change their approach in the securing of information and remedy this situation?”
At the start of the crisis, security departments prepared to let people out. Now, they will have to prepare to let people in again.
Chris Gould:
A crucial element in the coming back of workers to the office has to be the remobilisation of workers on security monitoring and the examination of breaches that have occurred while IT departments were distracted. People with forensic breach detection skills will be in high demand to find indicators of compromise on devices before deeming them safe to be re-included in the office.
Kalita Partners:
What are your views on the big fears of law firms and funds having their business held for ransom? We have seen a major ransomware attack on a high-profile American law firm last week where attackers were asking for a $40 millions ransom.
Chris Gould:
Ransomware is a crude tool in my opinion. It is a very opportunistic instrument - you send a link to everybody and wait to see who clicks on it.
The blunt force tool that is malware is really indiscriminate and organisations that fall for it like to say that they’ve been the target of a cyber-attack.
I call it bad IT cyber-hygiene and not a cyber-attack. These companies probably have obsolete systems they haven’t patched properly or a lot of legacy which can be the cause of other challenges.
Kalita Partners:
Are human elements important in allowing cyber-attacks to take place?
Chris Gould:
I used to teach consulting skills such as negotiation, influence assertiveness, etc. If you actually take all the skills you’ve learned to be a good business professional and turn them 180 degrees, you create the ability to manipulate people to get them to do what you want without them really being aware of it.
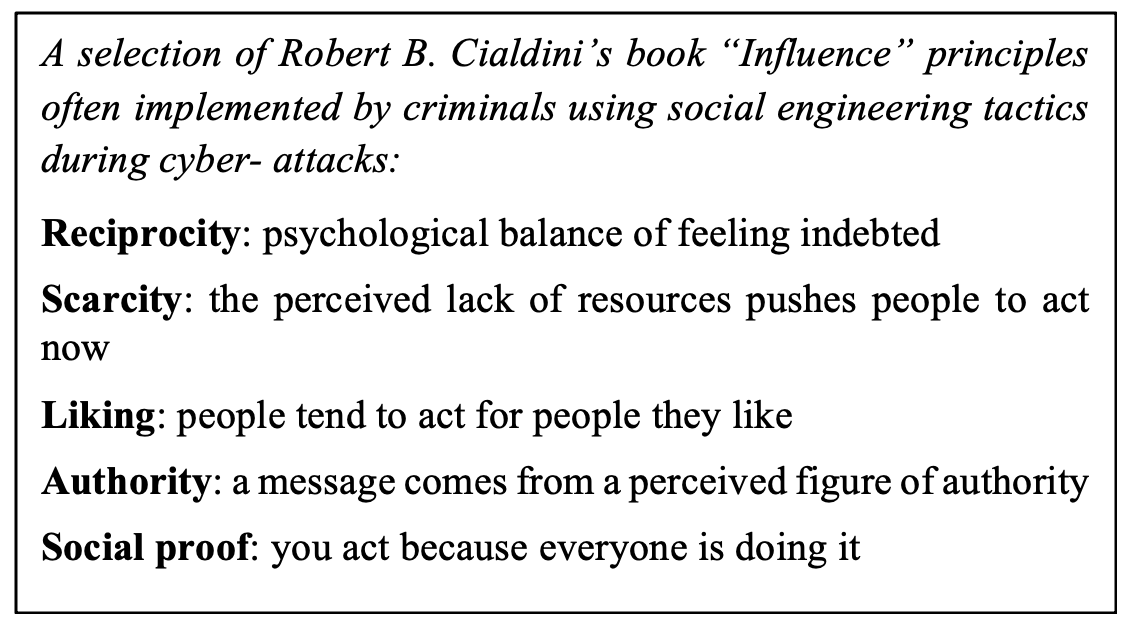
I strongly recommend a book called Influence by Robert B. Cialdini, which talks about the subconscious elements that allows us to be influenced. A number of elements present in this book are used by social engineers and we should be aware of this.
Kalita Partners:
What is everybody waiting to hear about when it comes to cyber-security and COVID-19?
Chris Gould:
From my perspective, the COVID-19 will have two impacts on businesses. One is the enforced digitalisation of work, which has led to the weakening of organisations’ security infrastructures to allow workers to work remotely. Now is the time to secure the elements opened up quickly to take back control of security.
The other impact is the need to forensically look at devices to catch everything that happened when we were distracted by making sure the business was still running.
Alexander Pisemskiy:
I think Chris summarised very well the lessons to learn from this crisis. We can probably rethink how we operate our companies and the security of the IT infrastructure. We have to change how we are organised and move to an “untrusted devices” norm- treat all devices as untrusted and adapt so that employees can still work.
This change of perspective will require companies to use new tools and manage them differently, but it will increase their agility.
* * *
Chris Gould is a Senior Adviser at Kalita Partners
Alexander Pisemskiy is the Forensic Technology Leader and co-founder of Kalita Partners
Copyright Kalita Partners 2020

